What is SSPM? Software-as-a-Service (SaaS) security posture management (SSPM)
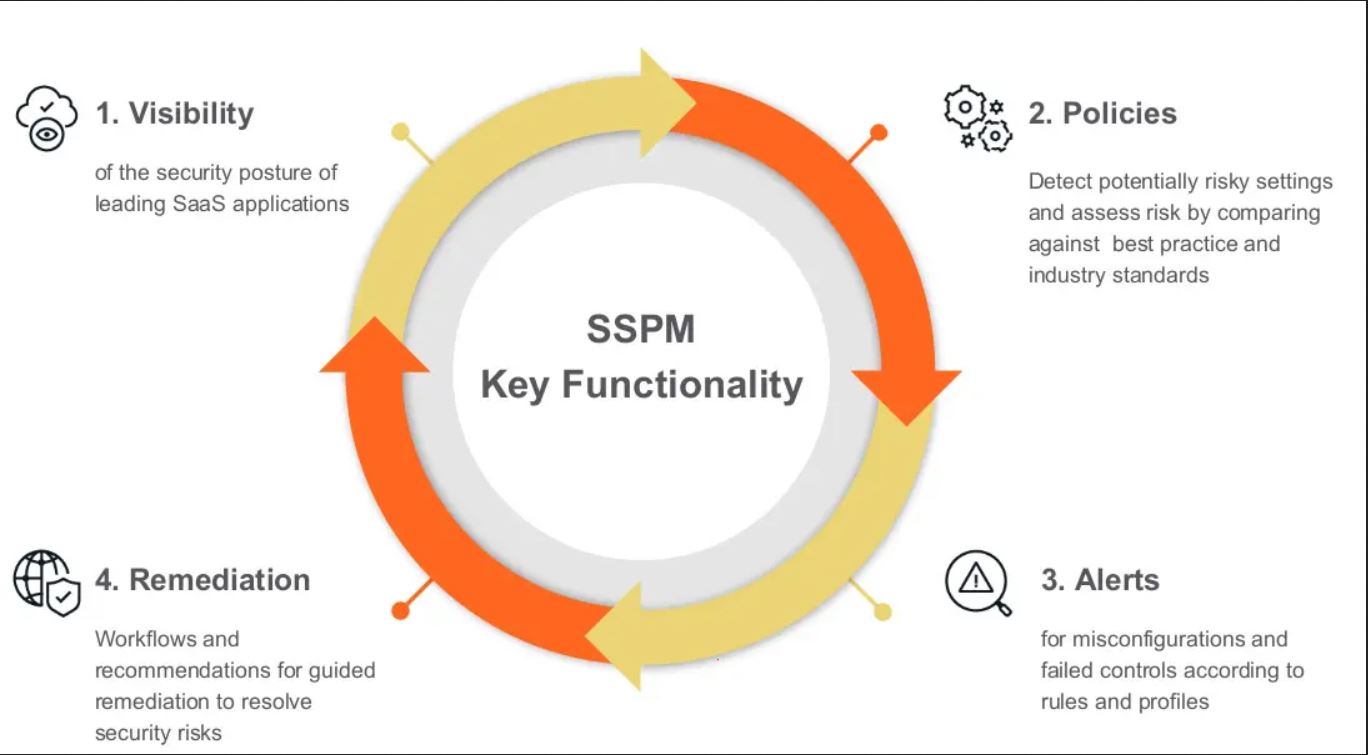
Software-as-a-Service (SaaS) security posture management (SSPM) is a category of automated security tools for tracking security threats in SaaS applications.
SaaS security posture management (SSPM) is a type of automated security tool for monitoring security risks in software-as-a-service (SaaS) applications. SSPM identifies misconfigurations, unnecessary user accounts, excessive user permissions, compliance risks, and other cloud security issues.
Unlike cloud security posture management (CSPM), which takes a holistic view of an organization’s entire cloud infrastructure, SSPM focuses on SaaS applications — for example, Salesforce, Slack, and Office 365. Businesses that rely solely or mostly on SaaS, as opposed to using cloud infrastructure such as platform-as-a-service (PaaS) and serverless computing, may get more value out of SSPM than CSPM.
What is SaaS security posture?
Security posture is a term that refers to a system’s readiness to mitigate attacks. SaaS security posture is that same concept applied to SaaS applications, which are hosted remotely in the cloud instead of locally on an internal network.
This differentiates SaaS security from traditional network security: Because SaaS applications are hosted remotely, they are largely outside of an organization’s control. And they are accessed over the Internet, from almost any device, which increases the risk of an unauthorized user accessing data or accidentally releasing data into the wider Internet.
To avoid these outcomes, SSPM tools help eliminate security gaps in SaaS applications. They automatically detect security risks to eliminate the threat posed by manual errors in setup.
How does SSPM work?
SSPM regularly analyzes an organization’s SaaS apps in the following areas:
- Configurations: SSPM looks for errors in the security setup that could leave data exposed to the Internet.
- User permission settings: SSPM reviews what users are allowed to do within the organization’s SaaS apps. As part of this process, some SSPM tools detect inactive and unnecessary user accounts. Pruning user accounts helps reduce the number of attack vectors.
- Compliance: SSPM identifies security risks that could put an organization out of compliance with data security and privacy regulations.
SSPM sends automated alerts to security teams when it discovers risks in these areas. Some SSPM tools can also automatically mitigate many of these risks.
How does SSPM contrast with CSPM?
Instead of focusing on SaaS applications, CSPM analyzes entire cloud deployments at multiple levels of the computing stack. CSPM scans:
- Infrastructure-as-a-service (IaaS)
- PaaS
- SaaS
- Containers
- Serverless code
CSPM tools may also have some capabilities that SSPM tools do not have, such as:
- Vulnerability detection: CSPM identifies vulnerabilities that attackers can exploit in cloud software.
- Incident response: Some CSPM tools can automatically take action to mitigate in-progress security incidents.
Follow the Firewall Firm – Cyber Security News channel on WhatsApp: https://whatsapp.com/channel/0029VaJ6lsZ77qVZJfDCPt15
 Firewall Security Company India Complete Firewall Security Solutions Provider Company in India
Firewall Security Company India Complete Firewall Security Solutions Provider Company in India